2015 - User Data Manifesto 2.0 - Frank Karlitschek, Hugo Roy, Jan-C. Borchardt
Texto
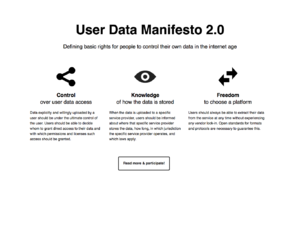
This manifesto aims at defining users’ fundamental rights to their own data [1] in the Internet age. People ought to be free and should not have to pay allegiance to service providers.
0. User data means any data uploaded by a user for his or her own use [2].
Thus, users should have:
1. Control over user data access
User data should be under the ultimate control of the user. Users should be able to decide whom to grant direct access to their data and with which permissions and licenses such access should be granted [3].
Data generated or associated with user data (e.g. metadata) should also be made available to that user and put under their control just like the user data itself [4].
2. Knowledge of how user data is stored
When user data is uploaded to a specific service provider, users should be informed about the geographic location that specific service provider stores the data in, how long, in which jurisdiction that specific service provider operates and which laws apply [5].
This point is not relevant when users are able to store their own data on devices in their vicinity and under their direct control (e.g. servers) or when they rely on systems without centralised control (e.g. peer-to-peer)[6].
3. Freedom to choose a platform
Users should always be able to extract their data from the service at any time without experiencing any vendor lock-in [7].
If users have these rights, they are in control of their data rather than being subjugated by service providers.
Many services that deal with user data at the moment are gratis, but that does not mean they are free (as in freedom). Instead of paying with money, users are paying with their allegiance [8] to the service providers so that they can exploit user data (e.g. by selling them, licensing them or building a profile for advertisers).
Surrendering privacy and other rights in this way may seem to many people a trivial thing and a small price to pay for the sake of convenience that these Internet services bring.
Service providers have thus been unwittingly compelled to turn their valuable Internet services into massive and centralised surveillance systems. It is of grave importance that people understand and realize this, since it forms a serious threat to the freedom of humanity and to the privacy of each individual.
Ultimately, to ensure that user data is under the users’ control, the best technical designs include peer-to-peer or distributed systems, and unhosted applications. Legally, that means terms of service should respect users’ rights and give them the possibility to exercise the datarights [9] defined in this manifesto.
Notes
[1] “Data rights” are a new set of rights that people should have but are not recognised by law (yet). They are unlike:
a. copyright, because data rights apply to data whereas copyright applies to “works” (typically, works of art).
b. data protection, because data rights apply for the user uploading data, not for the person who is the subject of the personally identifiable data.
So data protection and data rights complement each others and some data is at the intersection of both of these rights.
[2] Examples of user data include:
- the files a user is syncing through multiple devices or sharing with a friend
- a library of photos, books or other files a user uploads from their device in order to be able to read, view or modify online
- data generated by a user's device (like a connected watch or theromstat) and sent to a server
- a user's search engine queries, if they are logged as such
[3] When users have control over the upload of their data, data intended to be privately shared should not be accessible to the service provider, nor shared with governments.
That means the right to use cryptography should never be denied.
That also means that when users do not have full control over the upload of their data (e.g. if they don't use cryptography before uploading) a service provider should not:
a. force users to disclose private data (including private correspondence) with them, nor
b. impose licensing conditions (e.g. on copyright, or personal data exploitation) that go beyond what is necessary for the purpose of running the service.
When users make data available to others, whether to a restrictive group of people or to large groups, they should be able to decide under which permissions they grant access to this data. However, this right is not absolute and should not extend over others’ rights to use and exploit the data once it has been made available to them. What’s more, it does not mean that users should have the right to impose unfair restrictions to other people. In any event, technical systems should not be designed to enforce such restrictions (e.g. through DRM).
[4] Some services allow users to submit data with the intention to make it publicly available and usable by all. Even in these cases, some amount of user data is kept private (e.g. metadata or social graph data). The user should also have control over this data.
[5] When users use centralised services that uploads data to specific storage providers instead of relying on peer-to-peer systems, it is important to know where the providers might store data because they could be compelled by governments to turn over data they have in their possession.
[6] Users should not rely on centralised services. Peer-to-peer systems and unhosted applications are a means to that end. In the long term, all users should be able to have their own server with Free Software.
[7] Users should not get stuck into a specific technical solution. This is why they should always be able to leave a platform and settle elsewhere.
Open standards for formats and protocols are necessary to guarantee this.
Obviously, without the source code of the programs used to deal with user data, this is impractical. This is why programs available to exploit exported data should be available under a Free Software (Open Source) License.
[8] Bruce Schneier. The Battle for Power on the Internet (extract):
I have previously characterized this model of computing as "feudal." Users pledge their allegiance to more powerful companies who, in turn, promise to protect them from both sysadmin duties and security threats. It's a metaphor that's rich in history and in fiction, and a model that's increasingly permeating computing today.
Medieval feudalism evolved into a more balanced relationship in which lords had responsibilities as well as rights. Today's Internet feudalism is both ad-hoc and one-sided. Those in power have a lot of rights, but increasingly few responsibilities or limits. We need to rebalance this relationship. In medieval Europe, the rise of the centralized state and the rule of law provided the stability that feudalism lacked. The Magna Carta first forced responsibilities on governments and put humans on the long road toward government by the people and for the people. In addition to re-reigning in government power, we need similar restrictions on corporate power: a new Magna Carta focused on the institutions that abuse power in the 21st century.
Today's Internet is a fortuitous accident: a combination of an initial lack of commercial interests, government benign neglect, military requirements for survivability and resilience, and computer engineers building open systems that worked simply and easily.
We're at the beginning of some critical debates about the future of the Internet: the proper role of law enforcement, the character of ubiquitous surveillance, the collection and retention of our entire life's history, how automatic algorithms should judge us, government control over the Internet, cyberwar rules of engagement, national sovereignty on the Internet, limitations on the power of corporations over our data, the ramifications of information consumerism, and so on.
Data is the pollution problem of the information age. All computer processes produce it. It stays around. How we deal with it -- how we reuse and recycle it, who has access to it, how we dispose of it, and what laws regulate it -- is central to how the information age functions. And I believe that just as we look back at the early decades of the industrial age and wonder how society could ignore pollution in their rush to build an industrial world, our grandchildren will look back at us during these early decades of the information age and judge us on how we dealt with the rebalancing of power resulting from all this new data.
https://www.schneier.com/blog/archives/2013/10/the_battle_for_1.html
[9] “Data rights” are a new set of rights that people should have but are not recognised by law (yet).
They are unlike:
- copyright, because data rights apply to data whereas copyright applies to “works” (typically, works of art).
- data protection, because data rights apply for the user uploading data, not for the person who is the subject of the personally identifiable data.
So data protection and data rights complement each others and some data is at the intersection of both of these rights.
Archivo
Archivo:User data manifesto.pdf
Contexto
Aparece en Varios autores. (2016). Manifestos For The Internet Age v0.8. M.Schmalstieg, B. Crevits, V.Kruug (Eds). Greyscale Press.
https://github.com/greyscalepress/manifestos/tree/master/content/manifestos
Enlaces
URL: https://userdatamanifesto.org/, https://owncloud.org/conf/
Wayback Machine: https://web.archive.org/web/20170420011142/https://userdatamanifesto.org/, http://web.archive.org/web/20160328021521/https://owncloud.org/conf/